IT is a technology company that works together with your business and help your business to grow. Our IT Services and solutions include IT consulting, development services, cloud solutions, hosting services, website designing, Apps development for all platforms including Windows, IOS and Android, SMS gateway services and IaaS, PaaS and SaaS offerings.

Web hosting from IT Company USA, for your Website to succeed
Are you looking for a fast web hosting provider with top-notch customer service, incredible prices, and better performance? Web hosting services from IT Company USA are credited with helping businesses succeed all over the world. We offer managed web hosting services that ensure your website is safe, dependable, quick and always available. In this fast-paced world, we ensure that any visitor of your website can use it conveniently.
30 days money back guarantee
Free migration & onboarding
Free Technical Support
|
Web Hosting |
Managed Wordpress Hosting |
|
|
FTP Hosting |
Your Email is your Identity, Use your Own Brand Name
When it comes to email hosting, you have a lot of options. Whether you are managing an online store, a simple website, or need to set up email accounts for your staff, email is a necessity. The email hosting services offered by IT Company USA are specifically created to meet your needs for secure and safe email hosting because your email reflects you.
A modern, scalable Website Design can increase your revenue
There are several methods to design a website and maintain the material on it, but when you use our web design and content management service, you get a professionally made website and a secure content management system that is tailored to your exclusive requirements.
Application Development Services that are innovative, clever, and scalable
Application development services help design, build, and evolve software. IT Company USA purely focuses on building unique, smart, and stable applications. We aim to develop affordable applications that are user-friendly, quick to load, reliable, and economical across all platforms. We build custom apps that align with modern business models.

IT Company USA is Developing user-friendly Web Applications
Poorly performing web apps cause 88% of the users to have negative feelings regarding the brand. Businesses frequently make the error of neglecting usability. An intuitive web application can improve the performance of your business, boosting your productivity and income. For your web app to be successful, an attractive appearance isn't all it takes--a successful web application also provides a seamless user experience for visitors.
Exceptional App Development Service
Reliable & Secure Web Apps development
App Integration to any Cloud Application
Open for Business, but not reaching your objectives?
Perhaps your business is falling short of your goals and aims. IT Company is here to help you increase your revenue. With more people using the internet to conduct their businesses, it's critical to establish a digital marketing plan for your sales. We can assist you in reaching your ambition through digital marketing. We assure you that we will support the growth of your business, and increase revenue for you.
7 days money back guarantee
Generate more leads & clients
Increase visibility on Social Media

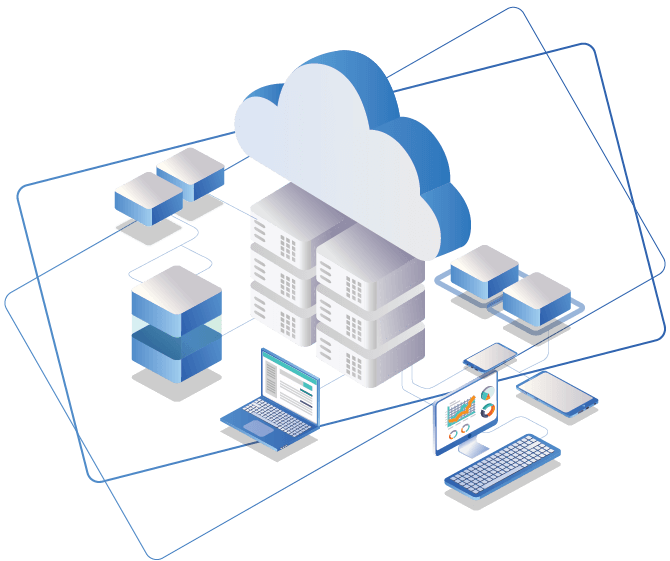
Let the Cloud help you in your Business Growth
IT Company USA allows organizations to transform their IT environment, making it more productive, flexible, and more collaborative with our cost-effective cloud services. We assist customers with our on-demand enterprise Cloud solutions and tools, as well as applications such as servers, storage, databases, software, and apps, among others.
AWS or Azure Cloud management services
Free migration & onboarding
Cloud flexibility and scalability
Defend your Website from Cyber Threats
Cyber attacks are a prevalent threat to businesses everywhere. Rather than thinking of a data breach as a possibility, enhance your security so that your website stays secure. IT Company USA’s security services empower our customers to improve their defences, accelerating detection and response. We can help you reshape your website security landscape and protect it from future online attacks. Our team of experts can also recover and repair your hacked websites, making them resilient to prevent future intrusions.
Secure your website & brand name
Free Review and Quote
Free Technical Support

PORTFOLIO
IT Company USA provides you with a wide range of services, specifically catered to your business needs. We aspire to uphold company standards for our customers' requests and ensure your continuous business growth.
FREQUENTLY ASKED QUESTIONS
Business automation is a process of managing information, data and processes to reduce costs, resources and investment. BPA increases productivity by automating key business processes through computing technology.
Business Automation System (BPA) is suitable for all types of businesses including finance or investment firm, manufacturing organization, banks, retailers, wholesalers, Schools or Universities, nonprofit organization, charity house, groceries, super markets, restaurants or even a local coffee shop. All you needs is imbedded technology system in your organization for smooth functions at all level.
Reduced business costs as double-handling and duplication is eliminated.
Business Automation System (BPA) is suitable for all types of businesses including finance or investment firm, manufacturing organization, banks, retailers, wholesalers, Schools or Universities, nonprofit organization, charity house, groceries, super markets, restaurants or even a local coffee shop. All you needs is imbedded technology system in your organization for smooth functions at all level.
Have more questions? Ask your question here
IT Company USA | Recent Blogs
You can find out more about IT Technology, Hosting, and Software News at our recent blogs
Our Clients
IT Company USA has been entrusted by acclaimed organizations around the globe for major IT solutions and services.